In today’s landscape, organizations of all sizes are increasingly adopting the default assumption that adversaries may already be persistent within their networks. This pragmatic perspective underscores the critical need and inherent value of an active segmentation program.
Segmentation introduces critical control points, regulating who and what can access the network environment and its applications. It also facilitates the creation of artifacts essential for reporting and compliance validation. Furthermore, segmentation significantly restricts the “blast radius” of an incident, greatly aiding incident response by clarifying the “who, what, and how” of an attack. Many readers might immediately think of Zero Trust, minimum privilege access, and the comprehensive accounting of every d…
In today’s landscape, organizations of all sizes are increasingly adopting the default assumption that adversaries may already be persistent within their networks. This pragmatic perspective underscores the critical need and inherent value of an active segmentation program.
Segmentation introduces critical control points, regulating who and what can access the network environment and its applications. It also facilitates the creation of artifacts essential for reporting and compliance validation. Furthermore, segmentation significantly restricts the “blast radius” of an incident, greatly aiding incident response by clarifying the “who, what, and how” of an attack. Many readers might immediately think of Zero Trust, minimum privilege access, and the comprehensive accounting of every device and session across their networks. However, based on years of working with and advising clients on segmentation, I’ve observed that overly ambitious goals often lead to implementation challenges and potential failure. The adage, “Don’t let perfection be the enemy of good,” is particularly relevant here.
I consistently approach the segmentation journey with my customers by framing it as a circular cycle. This cycle starts with visibility, progresses through identity context, policy selection, and policy enforcement, ultimately returning to enhanced visibility. See figure 1.
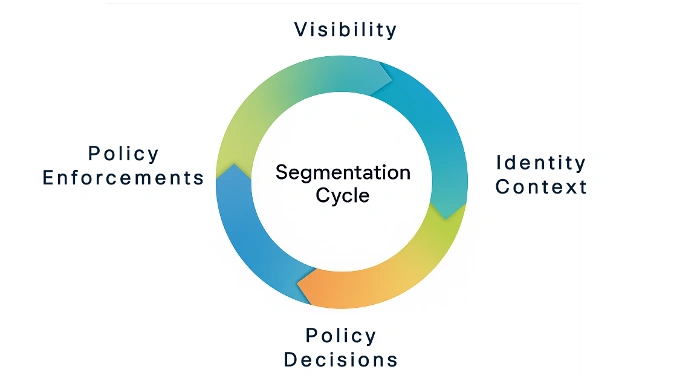 Fig. 1: The segmentation cycle
Fig. 1: The segmentation cycle
Visibility
The segmentation cycle both starts and ends with robust visibility. Gaining clear visibility into endpoints and network traffic within the environment is crucial for effective discovery. A critical initial step involves establishing a baseline by monitoring “normal” network behavior, utilizing tools like NetFlow data or monitor mode on Catalyst switches for passive endpoint profiling.
Each additional telemetry source further contributes to a more comprehensive understanding of the environment. The insights gained here guide policy creation as the deployment and support team’s abilities mature.
Identity Context
Identity can be represented in various forms, such as the VLAN a device connects to, a wireless SSID, IP address, MAC address, or information obtained through active or passive authentication.
Context, on the other hand, encompasses all other attributes that can positively or negatively affect that identity. For instance, if Mark is using his issued laptop, but its local firewall is disabled, the device’s state would be deemed “unhealthy.” These combined attributes collectively define the Identity Context.
Policy Assignment
Policy Assignment, often referred to as the Policy Decision Point (PDP) in NIST SP 800-207, represents the “what” in our segmentation cycle. It dictates what an identified user or endpoint is permitted to do.
This assignment can be dynamic, meaning the chosen policy is directly influenced by the Identity’s Context. Returning to our example, “unhealthy” Mark on his laptop will be assigned a different policy than “healthy” Mark, with the latter likely receiving broader access.
Policy Enforcement
Policy Enforcement is where the rules are put into action. As defined in NIST SP 800-207, a Policy Enforcement Point (PEP) is where the assigned policy for an identified user or endpoint is applied to permit or deny access to a target resource.
This stage represents the “how.” A target resource can be diverse—a website, an enterprise application, a file server, or any other asset to which the organization seeks to control access.
Returning to Visibility
The cycle’s return to visibility is paramount, as it provides actionable data confirming that policies are being enforced, helps pinpoint poorly aligned policies, and serves as a critical point for detecting unusual behavior and potential adversarial activities.
Why This Works
This framework offers a simple and repeatable approach applicable to any access scenario. The policies assigned can be directly aligned with business objectives and mapped to real operational use cases, providing a clear structure to facilitate segmentation adoption.
Policies can initially be coarse-grained, offering broad access permissions, and then evolve into more refined controls as the identity’s context develops.
Practical Applications
In upcoming weeks, I will explore practical applications of this approach across various segments of a typical enterprise network, including quick wins for achieving better segmentation without “boiling the ocean”:
- Remote user application access: Ensure secure connections for distributed teams.
- Secure branch (SD-WAN): Simplify segmentation across branches.
- Secure campus (wired/wireless): Improve segmentation for local users and devices.
- Traditional data centers: Enhance security of legacy infrastructure.
- **Cloud-native environments (Kubernetes, OpenShift, hyperscalers): **Apply segmentation in hybrid and multi-cloud environments.
Final Thoughts
One final, crucial piece of advice: do not embark on a segmentation journey without securing executive leadership support and an adequate budget. Like any significant undertaking, expect the unexpected. Challenges will arise that demand decisive action, and not every decision will garner universal agreement.
Remember: don’t let perfection be the enemy of progress.
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media