Custom links/Deep links are a great attack vector when analyzing mobile apps for security issues.
With static analysis you can enumerate the custom links either using the .plist file or uploading the Mach-O binary to ghidra and searching for strings but usually these come without the parameters. For example: you will only find deeplinks://custom which is not really helpful to analyze or fuzz them since the input parameters in the URI (for example- deeplinks://custom?param=secret) is what one should seek for to manipulate or fuzz.
I created a simple Frida script for apps built with ObjC and Swift to intercept custom links. Swift classes (like SceneDelegate.swift) can be hooked it seems with Frida ObjC classes. But it has to contain packagename.class...
Custom links/Deep links are a great attack vector when analyzing mobile apps for security issues.
With static analysis you can enumerate the custom links either using the .plist file or uploading the Mach-O binary to ghidra and searching for strings but usually these come without the parameters. For example: you will only find deeplinks://custom which is not really helpful to analyze or fuzz them since the input parameters in the URI (for example- deeplinks://custom?param=secret) is what one should seek for to manipulate or fuzz.
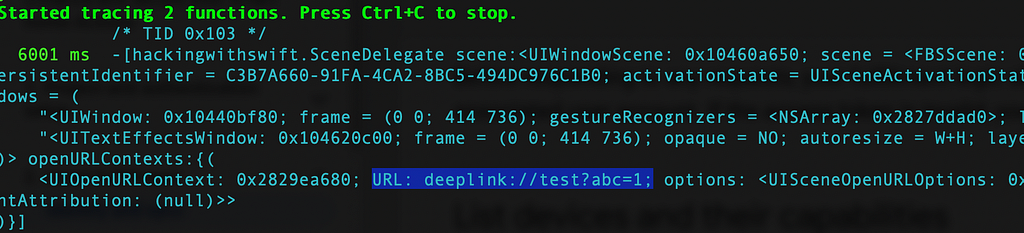
I created a simple Frida script for apps built with ObjC and Swift to intercept custom links. Swift classes (like SceneDelegate.swift) can be hooked it seems with Frida ObjC classes. But it has to contain packagename.class for example hackingwithswift.SceneDelegate where hackingwithswift is the package name.
So far, i have 2 functions that handles custom links, i’ll add more as i find.
https://github.com/In3tinct/frida-scripts/blob/main/find-customlinks-ios.js
Steps —
- List app process name you want to hook to
frida-ps -Uai
2. Hook into the method with the script
frida -U -N com.example.app -l find-customlinks.js
3. Just browse through the app/apps, check for app groups the target app has and browse through other app to the target app and see what data is being passed.
This can also be done with frida-trace but you would have to change the autogenerated .js file manually to capture the custom links.
frida-trace -U -N com.testin.hackingwithswift -m “-[*SceneDelegate scene:openURLContexts:]” -m “*[UIApplication applicationOpenURL*]”
iOS apps security — Intercepting custom deeplinks for security testing. was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.