If you’re a CTO, security architect, or IT manager, you know the truth: the perimeter security model is dead. In the modern cloud landscape, identity is the new perimeter. Trying to manage employee access, customer logins, and partner integrations across dozens of cloud apps using legacy tools or spreadsheets is not only inefficient, it’s a massive security vulnerability. A data breach, which costs an average of $4.88 million according to recent reports, is often traced back to a compromised identity. Furthermore, credential theft and compromises take an average of 292 days to fix completely, showcasing the severe, long-term operational impact of inadequate identity security. That’s why investing in robust Identity and Access Management (IAM) software isn’t optional—it’s …
If you’re a CTO, security architect, or IT manager, you know the truth: the perimeter security model is dead. In the modern cloud landscape, identity is the new perimeter. Trying to manage employee access, customer logins, and partner integrations across dozens of cloud apps using legacy tools or spreadsheets is not only inefficient, it’s a massive security vulnerability. A data breach, which costs an average of $4.88 million according to recent reports, is often traced back to a compromised identity. Furthermore, credential theft and compromises take an average of 292 days to fix completely, showcasing the severe, long-term operational impact of inadequate identity security. That’s why investing in robust Identity and Access Management (IAM) software isn’t optional—it’s critical business insurance and a cornerstone of any mature security program.
Identity and Access Management solutions are the foundational technology enabling organizations to verify identities, streamline access, and enforce the principle of least privilege across complex, distributed environments. Modern IAM encompasses everything from Single Sign-On (SSO) and Multi-Factor Authentication (MFA) to advanced Identity Governance (IGA) and Privileged Access Management (PAM). Choosing the right platform depends entirely on your organizational structure, regulatory requirements, and technical landscape—whether you are a B2B SaaS startup scaling rapidly, a massive enterprise managing hybrid infrastructure, or a compliance-heavy institution needing detailed audit trails. We’ve analyzed the market leaders to bring you a structured breakdown of the best IAM platforms available right now, categorized by their ideal use case.
Quick Look: Identity and Access Management Leaders
We have curated a list of the 12 most powerful and effective IAM solutions, covering key areas from developer-focused tools to highly specialized governance and privileged access suites.
SSOjet: Specialized B2B SaaS/Embedded SSO solution designed for rapid integration.
Okta Workforce Identity: Industry leader in cloud-native Workforce Identity Management.
Microsoft Entra ID (Azure AD): Essential identity platform for the Microsoft and Azure ecosystem.
SailPoint: The market standard for comprehensive Identity Governance and Administration (IGA).
CyberArk Workforce Identity: Best-in-class solutions for Privileged Access Management (PAM).
Ping Identity: Highly scalable solution for complex enterprise and partner access management.
Infisign: Focuses on AI-driven, Zero-Trust, and passwordless authentication technologies.
OneLogin (By One Identity): User-friendly and rapid deployment IAM suited for mid-market growth.
IBM Security Verify: Robust IAM for enterprises with complex, hybrid cloud and on-premise environments.
ManageEngine AD360: Simplified management and auditing tool specializing in Active Directory environments.
Oracle Identity Management: Enterprise-grade scalability with flexible deployment options for Oracle users.
SecureAuth: Unified platform offering adaptive authentication for both workforce and customer identity.
Quick Comparison:
| Tool Name | Best For | Free Plan/Trial | Starting Price |
|---|---|---|---|
| 1. SSOJet | B2B SaaS needing rapid Enterprise SSO/SCIM deployment | Free Developer Sandbox | Custom Quote (Based on enterprise connections) |
| 2. Okta Workforce Identity | Robust, cloud-native Workforce IAM with vast application integration | 30-Day Free Trial | ~$2–$5/user/month (Per feature module) |
| 3. Microsoft Entra ID | Organizations heavily invested in Microsoft/Azure ecosystem | Free Tier (Basic SSO/MFA) | Varies (P1/P2 or M365 Licensing) |
| 4. SailPoint | Large enterprises prioritizing Identity Governance & audit trails | Demo/Proof of Concept | Custom Enterprise Quote (Project-based) |
| 5. CyberArk Workforce Identity | Securing high-risk admin accounts (Privileged Access Management) | Demo/Proof of Concept | Custom Enterprise Quote (Module-based) |
| 6. Ping Identity | Large enterprises with high transaction volumes & complex partner access | Free Trial Available | Custom Enterprise Quote |
| 7. Infisign | Organizations focused on AI-driven, Zero-Trust security | Free Trial Available | Custom Quote (Subscription Model) |
| 8. OneLogin | Mid-market companies needing quick SSO/IAM deployment | 30-Day Free Trial | ~$5/user/month |
| 9. IBM Security Verify | Enterprises with complex hybrid cloud & on-premise setups | Free Trial Available | Custom Enterprise Quote |
| 10. ManageEngine AD360 | Windows-heavy IT environments and Active Directory management | 30-Day Free Trial | ~$595/year (Per technician/domain) |
| 11. Oracle Identity Management | Enterprise scalability & flexible deployment | Trial Available | Custom Enterprise Quote (Complex Licensing) |
| 12. SecureAuth | Unified Workforce (W-IAM) & Customer (CIAM) identity platform | Demo Available | Custom Enterprise Quote |
The 12 Best Identity and Access Management (IAM) Software Solutions
1. SSOJet
Best For: B2B SaaS Companies needing to quickly add Enterprise SSO/SCIM without rebuilding their authentication system.
SSOJet is a specialized Identity Provider (IdP) intermediary or "SSO accelerator" built specifically for modern B2B SaaS applications. Unlike traditional IAM solutions that focus on internal workforce management, SSOJet focuses squarely on the unique pain points faced by SaaS companies attempting to close large enterprise contracts that mandate SAML (Security Assertion Markup Language) or OIDC (OpenID Connect) SSO. Its core value proposition is speed-to-market. By integrating with existing authentication systems—be it Auth0, Firebase, or a custom database—SSOJet allows developers to offer enterprise-grade single sign-on capabilities in days, often going live in less than a week, a timeline that is impossible for traditional in-house development.
The platform provides a crucial self-serve portal where enterprise customers can easily configure their own Identity Provider settings (metadata, certificates) without requiring intervention from the SaaS vendor’s IT or engineering team. This self-service functionality significantly streamlines customer onboarding and reduces friction in the sales cycle. Furthermore, for B2B contracts where compliance is mandatory (e.g., SOC 2 Type II, HIPAA, GDPR), SSOJet provides built-in readiness, helping SaaS companies meet security mandates faster. It also supports SCIM (System for Cross-domain Identity Management), allowing for automated user and group provisioning and deprovisioning, a key requirement for enterprise efficiency and security hygiene.
SSOJet is highly attractive to developer-focused teams due to its clean APIs, comprehensive documentation, and non-intrusive design. It functions as an intermediary layer, meaning the SaaS application never needs to fully refactor its core authentication logic, minimizing development risk and ongoing maintenance burdens. This contrasts sharply with building SSO functionality from scratch, a task that often consumes multiple engineering sprints and becomes a continuous maintenance headache as IdP specifications evolve. By offloading this complexity to a specialized service, SaaS companies can focus their engineering resources on core product development while retaining the ability to serve the most security-conscious enterprise clients.
The acceleration of the sales process is arguably the most significant benefit of utilizing SSOJet. Security compliance, particularly the availability of SSO and SCIM, frequently becomes the last hurdle in closing major B2B deals. Having a ready-to-deploy, compliant solution like SSOjet shortens the gap between pilot and contract signing, directly impacting revenue realization. This specialized focus on embedded, developer-friendly enterprise SSO separates it from broad workforce IAM tools like Okta or Entra ID, positioning it as an essential growth tool for SaaS products targeting mid-market and enterprise segments. Check out SSOjet to see how they integrate with existing auth stacks.
Pros & Cons
| Pros | Cons |
|---|---|
| Rapid Deployment: Go live with enterprise SSO (SAML/OIDC) in days, not months. | Specialized focus; lacks the broader Workforce Identity Governance features of larger suites. |
| Non-Intrusive Integration: Works alongside existing systems (Auth0, Firebase, etc.). | Pricing scales with enterprise customer connections — needs careful financial modeling. |
| Enterprise Closing Tool: Compliance readiness (SOC 2 Type II, GDPR, HIPAA ready) accelerates B2B sales. | Primarily targeted at developers/SaaS companies; not ideal for internal workforce identity management. |
| Developer Focus: Clean APIs, great documentation, supports modern serverless/cloud stacks. | Limited advanced PAM or Zero Trust Network Access features due to its focused scope. |
| Self-Serve Portal: Lets enterprise customers configure their own IdP, reducing vendor IT workload. | Requires strong developer knowledge for initial setup and integration. |
Actionable Advice
For SaaS CTOs, utilize SSOJet’s developer sandbox environment immediately upon identifying the need for enterprise SSO. Integrate it during a proof-of-concept phase with a key prospect. This allows you to demonstrate compliance and technical readiness without committing significant internal engineering resources until the contract is secured. Ensure your SCIM implementation is thorough, as automated provisioning is often the second most requested feature after SAML SSO.
Pricing
Free/Trial Plan: Offers a 30-day Free Trial with no credit card required, providing access to core features including unlimited organizations, MAUs, logins, and users, along with passwordless authentication (Passkeys, Google, Microsoft, Slack login).
Paid Plans: The primary plan, Scale (or Business Pro), includes all core features plus Directory Sync (SCIM), custom branding, enhanced attack protection, and standard support. Pricing is based on a Custom Quote, determined by the number of enterprise connections/organizations integrated.
Enterprise Plan: Available via a Custom Quote ("Talk to an expert") for organizations needing a secure, dedicated private cloud, custom SLAs (99.9999% uptime), whitelabel APIs, and advanced compliance (ISO 27001, SOC2, HIPAA/BAA).
2. Okta Workforce Identity
Best For: Businesses seeking robust, highly integrated, cloud-native Workforce IAM and seamless app access.
Okta is synonymous with modern, cloud-first Identity and Access Management, serving as the trusted identity layer for thousands of organizations worldwide. As a highly integrated platform, it provides secure access to virtually any application, whether cloud-based (SaaS) or on-premise, leveraging its massive Application Network—the largest in the industry with over 7,000 pre-built integrations. Okta’s core strength lies in its ability to centralize user management, enabling Single Sign-On (SSO) across disparate corporate resources, greatly enhancing both employee productivity and IT control. The platform’s architecture is purely cloud-native, offering high availability and scalability without the burden of managing on-premise infrastructure.
Key security features include robust, Adaptive Multi-Factor Authentication (MFA), which evaluates user context—such as location, device health, and network—to dynamically adjust security requirements. This commitment to intelligent, risk-based access control aligns perfectly with Zero Trust principles. Beyond just authentication, Okta excels in Lifecycle Management, automating the provisioning and deprovisioning of users based on their employment status or role changes. This automatic process, often achieved via integration with HR systems like Workday or SuccessFactors, ensures that access is granted precisely when needed and immediately revoked when an employee leaves, mitigating a significant security risk.
Okta’s user experience (UX) is widely praised, offering employees a clean, personalized dashboard where they can access all their applications with a single click after initial authentication. This frictionless experience contributes significantly to user adoption and helps reduce help desk calls related to password resets and application access issues. For administrators, the centralized dashboard provides a comprehensive view of all identities, access policies, and security events, simplifying audit processes and compliance reporting. The platform’s commitment to innovation extends to passwordless authentication, allowing organizations to move beyond traditional password security altogether, relying instead on biometrics or hardware keys tied to the Okta Verify app.
The modular nature of the Okta platform allows businesses to start with core SSO and MFA and gradually incorporate more advanced features such as Access Gateway for securing legacy applications, Identity Governance (IGA), or Privileged Access Management (PAM) through recent acquisitions and product rollouts. This comprehensive, yet scalable, approach makes Okta an ideal choice for companies undergoing rapid digital transformation or managing complex, global workforces. By providing a unified identity fabric, Okta enables organizations to securely transition from legacy IT infrastructure to a modern, multi-cloud environment while maintaining stringent security standards. To explore their cloud identity solutions, visit Okta.
Pros & Cons
| Pros | Cons |
|---|---|
| Industry leader with thousands of pre-built integrations across SaaS and on-premise applications. | High cost for small to mid-sized businesses; pricing can become complex with multiple feature modules. |
| Robust Adaptive MFA and strong risk detection capabilities to enforce Zero Trust policies dynamically. | Requires dedicated planning and expertise for integrating complex Lifecycle Management workflows. |
| Excellent user experience, reliable platform uptime, and easy-to-use centralized administrative console. | Core governance (IGA) features might require additional modules compared to specialized IGA providers. |
| Comprehensive identity lifecycle management, automating user provisioning and deprovisioning. | Advanced troubleshooting across deep integrations can sometimes be time-consuming. |
| Cloud-native architecture offers inherent scalability and reduces infrastructure management overhead. | Subscription model costs can escalate quickly with premium features like threat insight. |
Actionable Advice
When implementing Okta, do not simply turn on SSO. Focus initially on deploying Adaptive MFA across all sensitive applications and integrating your primary HR system (HRIS) for automated Lifecycle Management. This step ensures that access is immediately secured and that the "joiner, mover, leaver" processes are fully automated, providing immediate security dividends and audit visibility.
Pricing
Free Plan: Offers a 30-Day Free Trial to test the platform’s features, including SSO and Adaptive MFA.
Paid Plans: Okta uses a modular licensing model, where pricing is determined per user per month based on the specific feature modules utilized (e.g., SSO, Adaptive MFA, Lifecycle Management, Advanced Security). Pricing generally starts in the range of $2–$5 per user per month for basic modules, with full suite implementation requiring a custom quote.
3. Microsoft Entra ID (Azure AD)
Best For: Organizations heavily invested in the Microsoft/Azure ecosystem requiring unified cloud security and identity management.
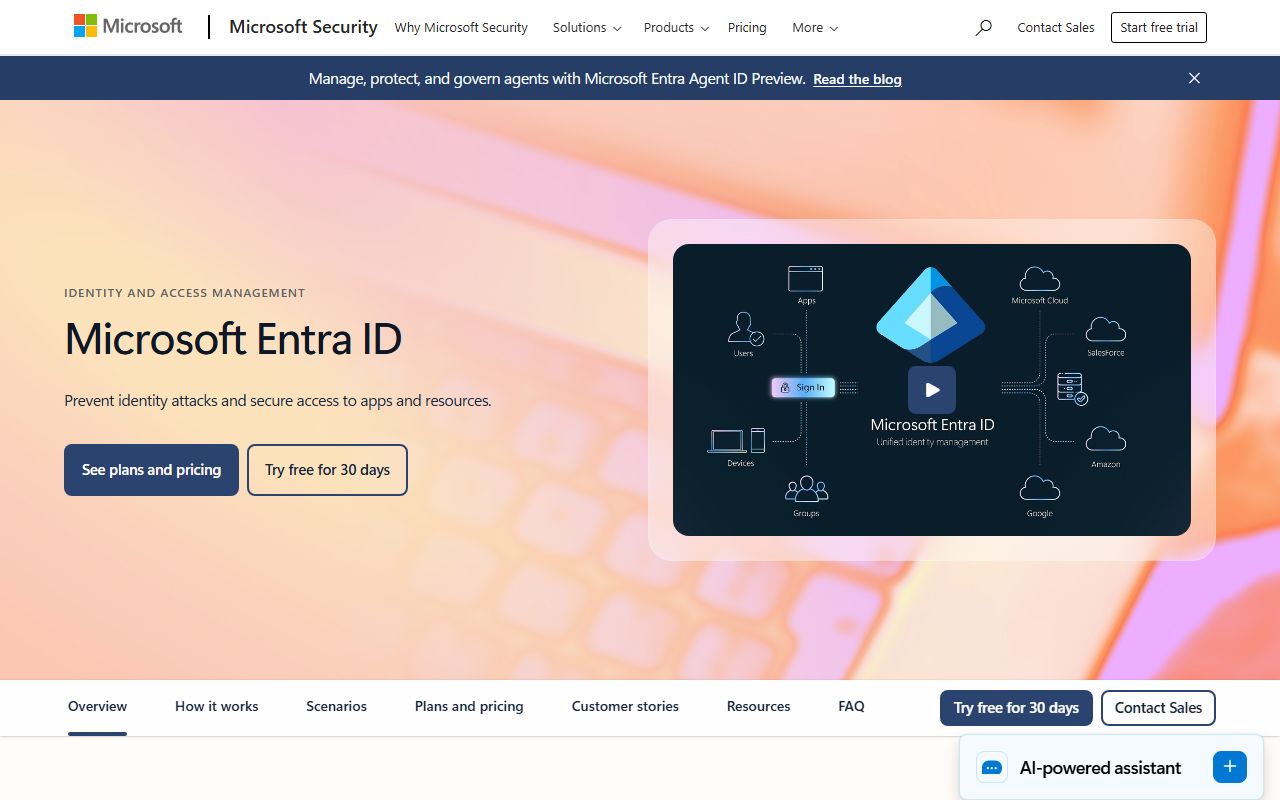
Microsoft Entra ID, formerly known as Azure Active Directory, stands as the cornerstone of identity management for organizations heavily reliant on the Microsoft cloud suite, including Office 365, Teams, and Azure services. Its seamless and deeply integrated nature within the Microsoft ecosystem is its primary competitive advantage. For companies running Windows environments, utilizing Microsoft applications daily, and deploying resources within Azure Cloud, Entra ID is often the default and most efficient identity solution. It functions as the universal control plane for access across all Microsoft properties and numerous third-party applications.
Entra ID provides highly granular access control through its signature feature: Conditional Access Policies. These policies allow IT administrators to define precise rules based on various factors—user identity, device compliance, network location, and real-time risk assessment—to determine if and how a user can access a resource. For example, a policy might mandate MFA only when an employee accesses a sensitive application from outside the corporate network, effectively implementing key Zero Trust principles. This level of policy granularity is essential for meeting modern regulatory and security requirements.
The platform is backed by the vast security intelligence apparatus of Microsoft, constantly leveraging threat data collected from billions of endpoints globally. This integration provides a powerful security layer, including identity protection features that automatically detect and remediate identity-based risks, such as compromised credentials or suspicious login activity. For compliance purposes, Entra ID offers robust reporting and audit trails, simplifying the process of demonstrating adherence to regulations like GDPR, HIPAA, or SOX, particularly regarding privileged access and access reviews.
While Entra ID excels within its native ecosystem, integration with non-Microsoft, third-party applications, though steadily improving, can sometimes be more complex or limited compared to vendor-agnostic platforms like Okta. Furthermore, organizations must navigate a complex licensing structure (often involving Premium P1 or P2 tiers) to unlock advanced features like sophisticated Conditional Access, Identity Governance, and Privileged Identity Management (PIM). Despite this complexity, for the millions of companies globally relying on Microsoft cloud services, Entra ID is indispensable for unified identity security and management. Learn more about the core security features at Microsoft Entra ID.
Pros & Cons
| Pros | Cons |
|---|---|
| Deep, seamless integration with Office 365, Windows, and Azure services, ensuring native functionality. | Significant vendor lock-in for organizations outside Microsoft ecosystem; limits third-party integration ease. |
| Conditional Access Policies are highly granular and effective for implementing Zero Trust security models. | Complex licensing tiers (Free, P1, P2) make cost prediction difficult; advanced features require premium subscriptions. |
| Strong security features backed by Microsoft’s security research and threat intelligence. | Integration with non-Microsoft apps can be cumbersome or require custom development compared to Okta. |
| Includes Privileged Identity Management (PIM) for securing admin roles via just-in-time access. | Administrative portal and feature organization can feel fragmented or overwhelming to new users. |
| Automatic compliance reporting and identity protection leveraging global threat analysis. | Reliance on Azure ecosystem; less appealing for pure AWS or Google Cloud environments. |
Actionable Advice
If you have Entra ID P2 licensing, immediately configure Privileged Identity Management (PIM). This allows you to enforce Just-in-Time (JIT) access for administrative roles, granting elevated permissions only when explicitly requested and for a limited time. This dramatically reduces the window of exposure for high-value accounts, which are prime targets for attackers.
Pricing
Free Plan: Included with all Azure, Dynamics 365, Intune, and Microsoft 365 subscriptions, offering basic Single Sign-On (SSO) and Multi-Factor Authentication (MFA) features.
Microsoft Entra ID P1: Starts from $6.00 per user/month (standalone, pricing varies with M365 bundles). Includes Conditional Access, dynamic groups, automated user provisioning to SaaS apps, and advanced security reports.
Microsoft Entra ID P2: Starts from $9.00 per user/month (standalone, pricing varies with M365 bundles). Includes all P1 features plus advanced Identity Protection (risk-based Conditional Access), Privileged Identity Management (PIM) for Just-in-Time access, and advanced Identity Governance features (access certifications, lifecycle workflows).
Microsoft Entra Suite: Includes all P2 features plus advanced Secure Access Services Edge (SASE) capabilities (Internet Access and Private Access). Pricing is custom/quote-based.
4. SailPoint
Best For: Large enterprises prioritizing comprehensive Identity Governance, audit, and risk management across complex environments.
SailPoint is the established market leader in Identity Governance and Administration (IGA). Unlike IAM solutions focused solely on delivering SSO/MFA, SailPoint’s core mission is to manage and govern who has access to what, why, and for how long across the entire enterprise estate—including applications, data, and infrastructure. It serves as the authoritative source for access policy, enabling organizations to manage the full identity lifecycle from initial onboarding ("joiner") to role changes ("mover") and final departure ("leaver"). This meticulous control is critical for maintaining security posture and satisfying stringent regulatory requirements.
The power of SailPoint lies in its ability to automate two historically cumbersome tasks: access certifications and compliance reporting. By analyzing user entitlements and comparing them against defined policies (Role-Based Access Control or Attribute-Based Access Control), SailPoint automatically identifies access outliers and risks. It then facilitates regular access reviews (certifications) required by regulations like SOX or HIPAA, providing managers with clear data on current access entitlements and requiring them to approve or revoke access privileges, creating an immutable audit trail. This automation saves hundreds of IT hours annually and drastically improves audit readiness.
SailPoint’s Identity Security Cloud leverages artificial intelligence and machine learning to offer predictive governance capabilities. It can analyze peer group access patterns to recommend appropriate access for new employees (a feature known as ‘peer group analysis’) and flag potentially toxic combinations of access privileges—such as the ability to both create a vendor and approve payments—before a breach or regulatory violation occurs. This proactive approach moves organizations beyond reactive security and into true preventative risk management.
SailPoint is typically deployed in large, highly regulated enterprises (finance, healthcare, government) that operate complex, heterogeneous IT landscapes, often involving multiple legacy systems alongside modern cloud apps. While it integrates with SSO providers like Okta and Entra ID for authentication delivery, its primary role is the oversight and governance layer above the authentication infrastructure. Implementing SailPoint is a significant undertaking, requiring specialized expertise, but the result is a unified, auditable, and resilient system of record for identity governance. Discover their full governance suite at SailPoint.
Pros & Cons
| Pros | Cons |
|---|---|
| Market leader in Identity Governance and Administration (IGA), providing unparalleled audit depth. | Primarily focused on governance; requires integration with other tools for robust SSO/MFA enforcement. |
| Automates complex compliance checks and access certifications required by major regulations (SOX, HIPAA). | Complex configuration and steep learning curve; requires specialized IAM expertise and consultancy. |
| Provides complete identity lifecycle management, ensuring timely provisioning and revocation across apps. | Higher cost structure, targeting large, compliance-heavy enterprises with significant budgets. |
| Advanced AI/ML-driven peer group analysis simplifies access review and detects toxic access combinations. | Deployment can be lengthy, often taking months due to complex integration with diverse/legacy systems. |
| Comprehensive identity risk scoring simplifies prioritization of users and access rights needing review. | Platform complexity can lead to governance fatigue if policies are not clearly defined and managed by teams. |
Actionable Advice
Before deploying SailPoint, conduct a thorough inventory of all existing application roles and entitlements. Do not attempt to govern chaos; focus first on defining a clear Role-Based Access Control (RBAC) model. Use SailPoint’s AI features early to identify common access patterns and potential segregation of duties (SoD) violations, making remediation part of the initial implementation phase.
Pricing
Free Plan: SailPoint offers a demonstration/Proof of Concept (POC) but does not offer a public free tier or self-service trial.
Paid Plans: SailPoint Identity Security Cloud is priced via a Custom Enterprise Quote. The cost is based on the total number of identities being managed (employees, partners, machines) and the specific modular capabilities needed, such as Identity Governance and Administration (IGA), Access Risk Management, or Data Access Security.
5. CyberArk Workforce Identity
Best For: Companies prioritizing Privileged Access Management (PAM) and securing high-risk administrative accounts.
CyberArk is the definitive global leader in Privileged Access Management (PAM). While general IAM focuses on the access rights of the entire workforce, CyberArk’s solutions are laser-focused on securing "privileged accounts"—those high-value, high-risk identities used by IT administrators, developers, third-party vendors, and critical machine accounts. These accounts, which include root access, domain administrators, and service accounts, are the primary targets in nearly all major data breaches, as they hold the keys to the kingdom.
CyberArk’s PAM solutions implement the principle of least privilege through multiple sophisticated mechanisms. Its secure credential vaulting system eliminates the need for administrators to know or store high-privilege passwords, instead injecting credentials automatically and securely upon request. This vaulting capability extends to securing machine identities and application secrets, ensuring that hardcoded credentials are removed from codebases. Furthermore, CyberArk enforces Just-in-Time (JIT) access, which grants privileged elevation only for the exact duration and specific task required, automatically revoking access afterward, drastically minimizing the attack surface.
A critical component of CyberArk’s offering is detailed session monitoring and recording. When an administrator or privileged user logs into a critical system (like a domain controller or sensitive database), CyberArk records the entire session—keystrokes, commands, and screen activity—providing an invaluable forensic trail. This not only aids compliance but serves as a powerful deterrent against insider threats and misuse of privilege. In the event of an incident, the session recording provides immediate, irrefutable evidence of the actions taken.
While CyberArk has expanded its portfolio into core Workforce Identity capabilities (SSO/MFA), its primary strength remains PAM. Organizations typically leverage CyberArk to secure their most sensitive assets—the administrative infrastructure, cloud console access, DevOps pipelines, and critical databases. Deploying CyberArk is a serious investment aimed at achieving maximum protection against catastrophic privilege misuse, making it mandatory for companies in defense, finance, and other sectors where security failure is unacceptable. Check out CyberArk’s PAM solutions and unified platform at CyberArk.
Pros & Cons
| Pros | Cons |
|---|---|
| Best-in-class solutions for Privileged Access Management (PAM), recognized globally as the industry standard. | Expensive licensing and implementation costs; typically requires large enterprise budgets. |
| Secure Credential Vaulting eliminates insecure password storage and management for admin accounts and secrets. | Deployment can be complex and extended, requiring specialized enterprise architecture and security knowledge. |
| Detailed session monitoring and recording for privileged user actions provide critical audit trails. | Limited general SSO/W-IAM capabilities compared to pure-play W-IAM providers, though improving. |
| Strong enforcement of the Principle of Least Privilege and Just-in-Time (JIT) access model. | Integration with highly customized or niche applications may require extensive API development and scripting. |
| Robust management of human and non-human identities, including securing API keys and DevOps secrets. | Managing the centralized policy engine requires continuous effort to keep up with organizational changes. |
Actionable Advice
Start your CyberArk implementation by identifying and vaulting your top ten most critical service and administrative accounts (e.g., Domain Admin, AWS Root User, Database Admin). Once these high-risk targets are secured, mandate Just-in-Time access for any human user needing elevated permissions, thereby shifting your security posture immediately toward proactive defense.
Pricing
Free Plan: CyberArk provides a demonstration or Proof of Concept (POC) for qualified enterprises to evaluate the platform.
Paid Plans: CyberArk operates on a highly customizable, module-based enterprise licensing model. Pricing is determined via a Custom Enterprise Quote, based on the number of privileged identities, the specific PAM solutions deployed (e.g., Secure Cloud Access, Secrets Management, Workforce Identity), and the desired level of security and support.
6. Ping Identity
Best For: Large enterprises requiring scalable, complex IAM solutions, especially those managing partner and vendor access.
Ping Identity, now part of the wider Thoma Bravo portfolio, is a veteran IAM provider known for its high-performance, enterprise-grade architecture capable of handling massive user bases and extremely high transaction volumes. Ping’s platform is highly flexible, supporting complex hybrid environments (both cloud and on-premise) and a wide array of identity standards, making it a robust choice for large, long-established organizations with diverse IT infrastructure. Its scalability and reliability are key reasons why it often powers the identity layer for major financial institutions and government agencies.
One of Ping Identity’s particular strengths is its comprehensive support for external identities, specifically in the domains of Customer Identity and Access Management (CIAM) and Partner/Vendor Access Management. For organizations that need to onboard millions of consumers or thousands of B2B partners securely, Ping provides the necessary resilience, customized login experiences, and advanced identity verification tools. Its CIAM suite includes features like delegated administration for partners and highly customizable user journeys to support branding and complex registration flows.
The platform utilizes advanced security capabilities, including adaptive authentication driven by real-time risk assessment. PingFederate and PingAccess continuously analyze user behavior, location, device characteristics, and network history. If a risk score exceeds a certain threshold, the system automatically challenges the user with a step-up authentication (MFA), thereby protecting resources without needlessly interrupting legitimate users. This behavioral analytics approach is critical for mitigating sophisticated attacks that bypass static security checks.
Ping Identity often appeals to organizations that need to secure a complex array of legacy applications alongside modern cloud services, thanks to its robust API security and access control features. While the implementation and configuration process can be more complex and require greater technical resources than some cloud-native competitors, its ability to manage identity at a massive scale and its strong focus on API-driven security make it a powerhouse for enterprises facing demanding performance and integration challenges. Explore their solutions for large-scale identity at Ping Identity.
Pros & Cons
| Pros | Cons |
|---|---|
| Highly scalable for massive enterprise deployments and high transaction volume environments. | Complex setup process requiring significant technical resources and specialized expertise. |
| Strong support for Customer Identity Access Management (CIAM) and secure Partner/Vendor Access Management. | Higher cost and inherent complexity make it less suitable for SMBs and mid-market companies. |
| Advanced risk assessment adapts security based on real-time behavior and context (adaptive authentication). | The UI/UX, while functional, is often considered less modern and intuitive than competing cloud-native platforms. |
| Robust API security and access management tools, critical for modern application development and microservices. | Ongoing maintenance and management require deep knowledge of networking and identity standards. |
| Flexible deployment options, supporting hybrid infrastructure (cloud, on-premise, containerized). | Achieving full feature parity across all legacy and new systems can be a prolonged project. |
Actionable Advice
If you choose Ping Identity due to its scalability for CIAM, focus heavily on utilizing the advanced federation capabilities. Use PingFederate to quickly establish trusted relationships with partners, allowing them to use their own IdPs while maintaining granular access policies managed by your Ping environment. This maximizes partner convenience while retaining centralized security control.
Pricing
Free Plan: Offers a 30-day Free Trial for both PingOne for Customers and PingOne for Workforce, including advanced authentication, user management, and risk features.
Paid Plans: PingOne for Workforce starts at $3 per user/month (Essential plan, based on a 5,000 user minimum annual contract) for SSO and Directory features. PingOne for Customers starts at $35,000 annually (flat rate, based on usage tiers) for CIAM Essential features. Adaptive MFA and advanced features are available in the Plus tiers or through modular add-ons like PingOne Protect.
7. Infisign
Best For: Organizations focused on cutting-edge, AI-driven, Zero-Trust security and eliminating traditional passwords entirely.
Infisign represents the next generation of Identity and Access Management, pushing the boundaries of security through advanced Zero-Knowledge Authentication and AI-driven workflow optimization. The platform’s philosophy centers on eliminating the weakest link in security—the password—by providing true passwordless authentication where login details never leave the user’s device and are never stored on company servers. This "Zero-Knowledge" approach drastically reduces the risk of mass credential exposure during a data breach.
A core differentiating factor of Infisign is its utilization of AI Access Assist, which the company claims can reduce the administrative workload for IT teams by up to 60%. This AI analyzes access requests, user roles, and organizational policies to automate approvals for routine tasks and flag highly unusual or risky access patterns for manual review. This automation streamlines operations while enforcing security policy far more consistently than human intervention alone. By integrating deep machine learning, Infisign moves beyond simple access checks to predictive and preventative security.
Infisign champions the Zero Trust model by implementing Adaptive MFA and continuous authentication checks across all access points. The platform supports a vast library of over 6,000 pre-built integrations, including support for legacy applications (Mobile Passcode and Web Authentication, MPWA) often overlooked by newer, purely cloud-focused providers. This broad compatibility allows enterprises to modernize their security posture without abandoning essential legacy systems.
For organizations seeking to leapfrog existing IAM technologies and adopt a truly modern, post-password security posture, Infisign provides the necessary tools. The platform emphasizes device integrity, ensuring that access is granted only to verified identities using known, compliant devices. Although newer to the market than decades-old competitors, its focus on cutting-edge cryptography and administrative efficiency makes it a compelling option for those prioritizing robust, forward-looking security architectures. Explore Infisign’s approach to eliminating passwords at Infisign.
Pros & Cons
| Pros | Cons |
|---|---|
| Zero-Knowledge Authentication ensures login details are never stored on company servers, minimizing breach impact. | Migration from entrenched password-based systems requires careful planning and change management. |
| AI Access Assist reduces admin workload by automating routine access approvals and risk flagging. | Passwordless technology requires dedicated employee training and robust internal support for adoption. |
| Over 6,000 pre-built integrations, including robust protection for legacy applications (MPWA Support). | Adoption rate and community support might be smaller than decades-old competitors like Okta or Entra ID. |
| Advanced Adaptive MFA and biometric support align with modern Zero-Trust mandates. | Comprehensive rollout of Zero-Knowledge authentication can be technically challenging across devices. |
| Focus on non-human identity management, critical for securing microservices and cloud infrastructure. | Integrating complex, highly customized on-premise solutions may require significant API work. |
Actionable Advice
When adopting Infisign’s Zero-Knowledge approach, establish a clear rollout plan for password elimination. Start with non-critical applications to build user confidence in biometric and device-based authentication. Leverage the AI Access Assist immediately to automate access requests for low-risk applications, demonstrating administrative efficiency gains early in the deployment process.
Pricing
Free Plan: A Free Trial is available, allowing organizations to test Infisign’s Zero-Knowledge and AI-driven passwordless authentication features.
Paid Plans: Infisign utilizes a Custom Quote (Subscription Model) tailored to the specific identity security needs of the organization, focusing on the deployment of its advanced modules (IAM Suite, UniFed CIAM, Adaptive MFA, PAM) and the utilization of its AI Access Assist features. Pricing requires direct contact with their sales team.
8. OneLogin (By One Identity)
Best For: Mid-market companies needing rapid deployment and a highly user-friendly, feature-rich general IAM/SSO solution.
OneLogin, now operating under the One Identity umbrella, is highly regarded for its blend of powerful, enterprise-grade features and its exceptionally clean, intuitive user interface (UI). It provides a comprehensive solution covering SSO, MFA, and Identity Lifecycle Management, often serving as the go-to choice for mid-market companies that require robust security without the staggering complexity or protracted implementation timelines associated with the largest enterprise suites. Deployment with OneLogin is often cited as significantly faster than competitors, enabling organizations to realize security and productivity benefits quickly.
A key strength of OneLogin is its focus on Real-Time Directory Sync and simplified Role-Based Access Control (RBAC). It maintains synchronization across multiple directory sources (Active Directory, LDAP, HR systems) in real-time, ensuring that identity data is always accurate and consistent. This capability is crucial for enforcing the principle of least privilege, as access changes are reflected immediately across all connected applications. The platform’s RBAC features are designed to be accessible, allowing IT teams to easily define job-based access policies rather than managing permissions application by application.
OneLogin’s security portfolio includes Adaptive Authentication, which uses machine learning to detect anomalous behavior and require step-up authentication when necessary. It provides a robust, centralized portal for both users and administrators. Employees benefit from a personalized launch portal for all their applications, improving productivity, while administrators receive unified reporting on access, auditing, and compliance across the entire connected estate.
While its integration library, though strong, may not be as voluminous as Okta’s, OneLogin provides critical connectors for the vast majority of enterprise and SaaS applications. Its positioning is ideal for growth-focused companies that have outgrown basic directory services but are not yet ready for the highly customized, governance-heavy investments required by systems like SailPoint. OneLogin delivers a mature, scalable, and manageable IAM foundation. Check out their rapid deployment capabilities at OneLogin.
Pros & Cons
| Pros | Cons |
|---|---|
| Simple, clean UI and quick implementation time, minimizing deployment overhead. | Fewer pre-built integrations compared to market leaders like Okta; may require custom API work for niche apps. |
| Strong focus on Role-Based Access Control (RBAC) synchronization simplifies managing complex permissions. | Limited advanced features in specialized areas like deep governance (IGA) or high-end PAM. |
| Excellent real-time synchronization across disparate user directories (AD, LDAP, HRIS). | Per-user costs can become relatively high for very large organizations scaling into hundreds of thousands. |
| Provides strong reporting and centralized compliance reports, simplifying audit preparation. | Doesn’t have the same market dominance or recognition as Microsoft or Okta for vendor negotiation leverage. |
| Comprehensive support model tailored to rapidly scaling mid-market businesses. | Mobile application experience is functional but sometimes lacks the polished feel of competitor applications. |
Actionable Advice
To maximize the benefit of OneLogin’s usability, invest time upfront in standardizing your user roles and groups. Use the powerful directory synchronization capabilities to link these standardized groups directly to application access policies. This approach ensures that when a new employee is hired into a defined job role, their access is provisioned correctly and instantly across all necessary applications.
Pricing
Free Plan: OneLogin offers a 30-Day Free Trial.
Paid Plans: Licensing is modular and user-based, starting with SSO at $2 per user/month. Additional modules like Advanced Directory ($2/user/month), MFA ($2/user/month), and Identity Lifecycle Management ($4/user/month) can be added to build a comprehensive IAM platform.
9. IBM Security Verify
Best For: Enterprises with complex, hybrid environments looking for IBM’s deep security insights and enterprise integration capabilities.
IBM Security Verify is an enterprise-class identity platform designed specifically to secure complex, hybrid IT environments that span legacy on-premise infrastructure alongside modern multi-cloud deployments. Leveraging IBM’s decades of experience in enterprise technology and security research, Security Verify offers advanced identity management solutions integrated with powerful threat intelligence and behavioral analytics. It is particularly well-suited for large, global organizations that cannot fully migrate to the cloud and require unified identity control across disparate systems.
The platform distinguishes itself through its advanced threat detection capabilities. Security Verify continuously monitors user behavior and access patterns, utilizing IBM’s advanced security intelligence to identify deviations from normal activity. This behavioral analysis enhances password safety and allows the system to detect subtle indicators of compromise that simple static checks might miss. If suspicious activity is detected, access can be automatically challenged or revoked in real-time, significantly mitigating the risk associated with stolen credentials.
Security Verify provides robust support for automated compliance reporting and audit trails, crucial for regulated industries. Its architecture supports sophisticated workflow integration, allowing organizations to automate provisioning, access requests, and approval processes based on custom business logic. This flexibility is essential for large enterprises with highly specific and nuanced operational requirements that standard off-the-shelf workflows cannot satisfy.
Furthermore, IBM Security Verify excels at bridging the gap between legacy applications and modern security standards. It allows organizations to extend strong authentication and SSO capabilities to older, on-premise systems that lack native support for modern identity standards. This hybrid management capability ensures that the organization maintains a consistent security posture across its entire infrastructure footprint, regardless of the age or location of the application. For organizations deeply embedded in the IBM ecosystem or seeking a solution tailored for complex, large-scale hybrid needs, Security Verify offers a highly capable and secure framework. You can find more details on its security capabilities at IBM Security Verify.
Pros & Cons
| Pros | Cons |
|---|---|
| Strong hybrid environment support, managing identities across cloud and on-premise systems seamlessly. | High implementation costs and substantial budget required; not ideal for smaller organizations. |
| Leverages IBM’s advanced threat intelligence and behavioral analytics for real-time risk scoring. | User interface can be complex or difficult for non-technical administrators compared to modern cloud tools. |
| Automated compliance reporting and comprehensive audit trails, integrated with enterprise GRC workflows. | Customer support responsiveness can sometimes be slow depending on issue complexity. |
| Enhanced password safety mechanisms and strong Multi-Factor Authentication options. | Integration with third-party applications sometimes lacks the "out-of-the-box" simplicity of competing platforms. |
| Robust workflow integration allows complex, customized approval and access request processes. | Requires specialized IBM knowledge and security expertise for full utilization and long-term maintenance. |
Actionable Advice
For hybrid deployment, prioritize using IBM Security Verify’s risk engine to protect the most vulnerable on-premise applications first. Instead of migrating them immediately, use the IBM solution to overlay modern adaptive authentication and logging onto these legacy systems, buying time for eventual modernization while immediately increasing their security posture.
Pricing
Free Plan: A Free Trial is generally available for eligible enterprises s