23.1.2026
OWASP Top 10 is a list of the ten most critical security risks for web applications, created by the Open Web Application Security Project (OWASP), and has been a central reference in application security for more than two decades. The list provides a common risk language for developers, security professionals, and technical leaders who build and protect software. The updated version for 2025 is now here, and it clearly shows how the threat landscape has evolved since 2021, when the previous version was released.
Briefly about what OWASP Top 10 is and what has changed
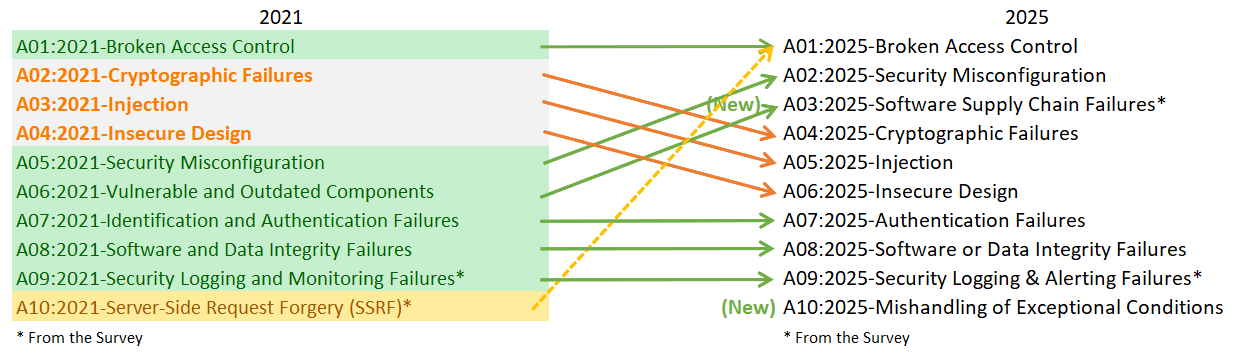
OWASP Top 10 2025 is out. The changes are fewer than many might have expected, but they are clear. The focus has shifted away from individual coding errors and toward systemic issues in how applications are built, configured, and operated.
The most interesting changes are not about new types of attacks, but about where flaws actually occur in modern applications. The data behind the 2025 list shows the same picture that many security teams already see in practice. Most serious findings come from access control, misconfiguration, and dependencies that are not fully under control.
OWASP Top 10 is updated approximately every three to four years, based on a comprehensive dataset of real vulnerability findings, contributions from the security community, and analysis of real-world attacks. The list is therefore less of a theoretical framework and more a distillation of what recurs in modern applications. The changes between each version are usually incremental, but they provide a clear picture of how risk areas and attack surfaces shift over time.
OWASP Top 10 2025
The final list of the ten most critical security risks in web applications looks like this:
- Broken Access Control
- Security Misconfiguration
- Software Supply Chain Failures
- Cryptographic Failures
- Injection
- Insecure Design
- Authentication Failures
- Software or Data Integrity Failures
- Security Logging and Alerting Failures
- Mishandling of Exceptional Conditions
Compared to 2021, the structure is familiar, but several categories have been moved, merged, or expanded. The changes reflect how real attacks are carried out today.
Software Supply Chain Failures
The most significant change in the 2025 edition is the introduction of Software Supply Chain Failures as its own category. This effectively replaces Vulnerable and Outdated Components from 2021 and significantly expands the scope.
The focus is no longer only on vulnerable libraries. The category covers the entire chain around the software: